Did you know that, just by using your web browser or having an email address, you already have a second identity in the digital world? We’re talking about your digital identity, and nowadays, it’s almost as important as your offline identity.
If you are looking to establish your business in cyberspace, position your personal brand or simply surf the web safely, you need to know the implications of your digital identity.
Therefore, we will tell you what your cyber identity consists of, what its implications are and how you can protect it from possible threats.
Table of Content
What is digital identity?
Your digital identity – also called identity 2.0 – represents your entire presence in the digital world. That is, from your social networks to your emails (yes, plural), and also your interactions, publications, social networks, pages or accounts you follow, etc.
Your identity also encompasses all your data, credentials and records. For example, passwords, IP address, devices, identity number, public records… absolutely everything is part of your digital identity.
Digital identity is created through your participation in online platforms. Also, through the use of web services and the generation of digital data, according to your interactions with the virtual world.
So, how is digital identity created?
Very simply, your identity exists from the moment you log in and start participating in online platforms. In other words, the 2.0 identity is built through data from the digital services you use and your interactions on the web.
However, the cornerstone of your digital identity is the information you provide to web services and platforms. And this data is collected, processed and used by:
- Companies.
- Search engines.
- Social networks.
- Government agencies.
- Public registries.
- Health systems.
On the other hand, the digital world also allows you to create -or project- more than one identity. For example, you can create an identity entirely dedicated to your personal brand and your professional environment. One for your personal accounts, and even another for online video games.
The importance of digital identity
It’s no secret that our world is more interconnected and digitized than ever. And it will be even more connected in the future. And that’s why checking the identity of users is becoming more and more challenging.
Therefore, knowing the implications of your digital identity and the different factors that can harm it is crucial for your online security.
To begin with, your digital credentials are essential to verify your true identity when talking about products and services on the web. It is also a fundamental requirement for public registries, banks and insurance companies, among many others.
As if that were not enough, and just like your real-world identity, your 2.0 identity is an essential part of your reputation. For example, to access better job opportunities and avoid inconveniences before the law.
And if you want to establish your business, company or personal brand in the marketplace, you need an impeccable and trustworthy reputation.
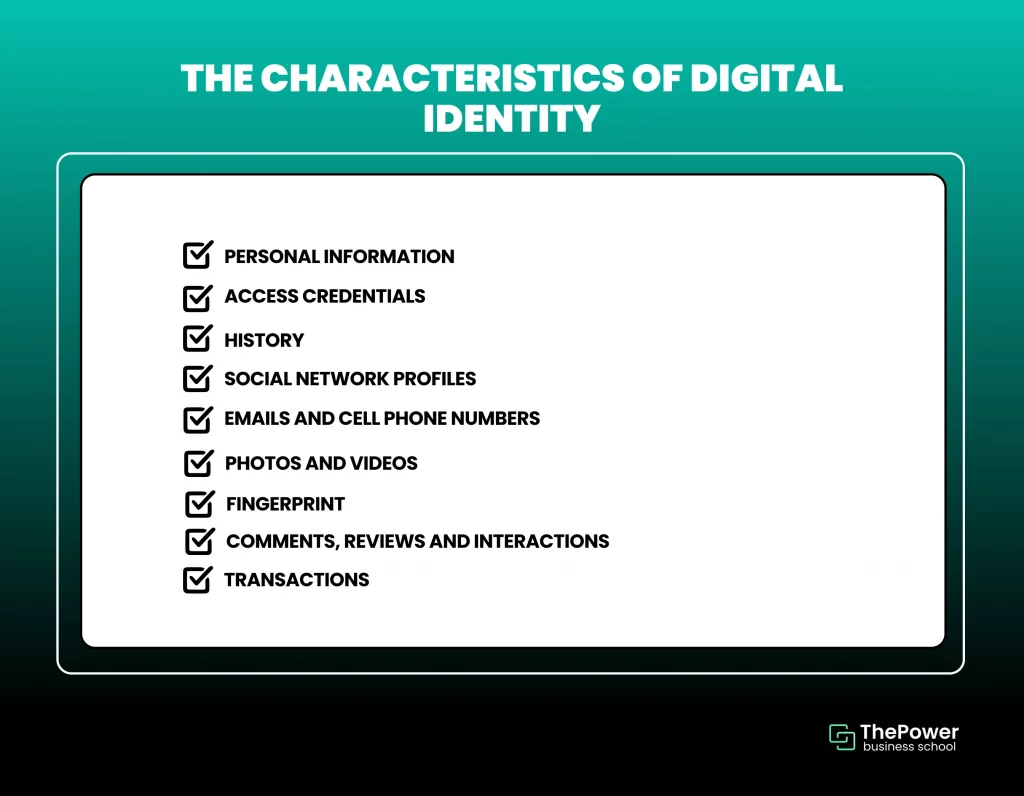
The characteristics of digital identity
These are some of the key elements of the digital identity:
1. Personal information
And by this we mean your identification, full name, date and place of birth, marital status, identity number, driving license, occupation, place of work….
These data are essential for absolutely everything outside the digital environment. Therefore, they are the fundamental basis of your identity in cyberspace, either to access products and services or simply to register your activity.
2. Access credentials
That is, passwords, accounts, profiles, codes, security protocols and interconnected devices.
These data are crucial for accessing all kinds of products and services on the web. But also for your official and legal records.
3. History
By this we mean the history that companies, websites, social networks, search engines and online stores keep in their records.
From the first moment you log on to these platforms, your IP address and your interactions are recorded and saved. Thus, online platforms can use this data to provide you with a better experience when you visit them again.
These are the famous cookies you see when you enter a website. And they can also be collected for advertising purposes if you agree to share them.
Your history is a key part of your identity on the web. All your activities and interactions on the web are part of your identity to search engines, websites and online services.
In other words, the records that companies, search engines, businesses, applications and government agencies keep are part of your 2.0 identity.
The data the sites collect allows them to assign you a unique identity within their databases. And thus, create a history for all your activities within their space.
In this way, websites and advertisers on the web can offer you a better user experience. That is, as long as you agree to share your cookies.
Note: cookies are a great example of how the sites you visit use your history to improve your user experience. Websites also share this data with advertisers so that they can provide you with more accurate ads.
4. Social media profiles
Social networks are the first thing that comes to mind when we talk about digital identity. They are one of the best representations of your identity in the digital world.
Unlike your history and cookies, the information you share on your social networks is easier to control. However, the information that other users share about you on social networks is far beyond your control.
For this reason, reputation is extremely valuable within social networks. And for many, the information on networks is more valuable than the information you share on other platforms.
On the other hand, social media is also one of the favorite and most versatile tools in digital marketing. And building a solid reputation on the networks is a must if you want your business or personal brand to position and maintain itself in the market.
5. Emails and mobile numbers
Both elements are key to access all kinds of platforms, accounts, profiles, products and services.
They are also essential resources for communicating with other users, whether they are visitors to your site, customers, companies, collaborators and potential partners, among others.
6. Photos and videos
Nothing is more revealing and speaks more about your identity -and your personality- than the content you share. But above all, photos and videos, whether on social networks or multimedia platforms.
And if we’re talking about your brand, nothing represents your brand’s identity and personality better than the content it offers users. Not to mention that audiovisual content is by far the most influential.
Therefore, audiovisual content should always be part of your marketing strategies. And in turn, you have to be careful with the content you share both in your professional networks and in your private life.
7. Digital footprint
This is one of the most inaccessible and difficult access keys for hackers to overcome.
Thanks to today’s technology, you can turn your fingerprint into one of your most important credentials. In other words, it can serve you both as a password and as a credential, verification method and recovery method; for example, if you lose your mobile device.
8. Comments, reviews and interactions
Your interactions on the web have an astronomical weight on your digital identity and reputation. In other words, your comments, opinions, interactions, reviews and criticisms will have a gigantic influence on users’ perception of you and your brand.
Likewise, your interactions are also elemental to your social media strategies. For example, to build a community, increase your number of followers and, of course, expand your customer base.
In turn, each of your interactions represents your digital identity and that of your brand. Therefore, you have to work them carefully to generate a positive perception in users and, above all, in your target audience.
9. Transactions
Transactions are a much more private part of your digital identity. However, they also play a critical role in your reputation, especially with banks, public records, insurers and digital wallets.
Think of this reputation as your credit history. The better your credit history, the better your financing opportunities and the less hassle you’ll have when it comes to large transactions.
You’ll also have a solid reputation on your side in case of complications with your accounts. And also in case of fraud attempts and identity theft, among other threats.
Most frequent attacks against digital identity
Now, your digital identity, being the key to access your accounts and profiles, has to be as protected and backed up as possible. And for this reason, we will tell you about some of the most common threats.
1. Phishing
Phishing is a technique used by hackers to trick people into divulging personal and confidential information, such as passwords, credit card numbers or sensitive account data.
How do they do it? Attackers impersonate reputable companies or organizations, and in most cases, use emails as their primary means of communication.
Phishing emails often contain fraudulent links that redirect to fake websites that mimic the appearance of legitimate websites. These fake sites capture your data, which is then used by cybercriminals to impersonate you.
2. Social engineering attacks
Social engineering is based on the manipulation and deception of individuals for the purpose of obtaining confidential information or inducing them to perform specific actions, such as providing access or disclosing data, among other possibilities.
Cybercriminals can employ social engineering through various means, such as phone calls, text messages, emails and social networking platforms, among other available methods.
To do so, they may adopt false identities, such as pretending to be employees of well-known companies, technical support service representatives, or they may even pose as friends in order to obtain personal information or login credentials.
They may even disguise themselves as technicians or delivery people to gain access to facilities and areas that are normally restricted.
3. Malware attacks
Hackers can use different types of malware, such as Trojans, keyloggers or ransomware, to infiltrate your devices and steal your personal information.
Trojans can allow remote access to the victim’s system. On the other hand, keyloggers record keystrokes to capture passwords and other information, while ransomware encrypts the user’s files and demands a ransom to recover them.
4 tips to protect your digital identity
And now, let’s look at how to prevent possible fraud and identity theft attempts on the web.
These 4 practical tips will help you minimize the risk of cyber-attacks and identity theft.
These tips are easy to apply and will help you preserve your identity from cyber-attacks and identity theft:
1. Prioritize password and authentication security
This step is easy to carry out, but we cannot overemphasise how important passwords are.
When choosing passwords for your online accounts, make sure they are strong and unique. Combine uppercase letters, lowercase letters, numbers and symbols to make them difficult to guess.
And please avoid using obvious information such as your middle name, date of birth or family members’ names.
To give your accounts extra security, we suggest enabling two-factor authentication (2FA) or two-step authentication whenever you can. This will provide you with an extra layer of protection, even if someone manages to crack your passwords.
You may also consider using a password manager to help you create and store unique and secure passwords for each online service.
2. Keep your software and data up to date
Make sure you keep your devices up to date, which includes operating systems, browsers and applications, whenever it is feasible to do so.
The logic behind this is quite clear: updates often fix weaknesses that could be exploited by cybercriminals.
Be cautious when dealing with messages, calls and emails, especially those that require personal information.
If you manage multiple accounts, platforms and profiles at the same time, we recommend that you continue to investigate possible social engineering strategies. This way, you will be better prepared to identify potential threats and reduce the chances of becoming a victim of phishing.
4. Adjust your privacy settings
Take a look at and adjust the privacy settings on your online accounts to decide what information you want to be public. Limiting the amount of personal data you share can help reduce the risk of identity theft.
Also, avoid using unprotected public Wi-Fi to do things like transactions or any activity that involves sensitive data. When possible, use secure connections and virtual private networks (VPNs) to keep your data safe.

These precautionary measures will allow you to be prepared for possible cyber-attacks and phishing attempts.
Your online identity will always play an essential role in your digital experience, both personally and professionally. That’s why we urge you to take the best possible care of your digital identity and not let your guard down in the face of potential threats.
Remember that in this technological age, your digital identity and credentials are extremely valuable.
Are you aware of the importance of digital identity? We’d love to hear your thoughts, so feel free to share them in the comments.






0 Comments